- Joined
- November 19, 2023
- Messages
- 2,718
- Reaction score
- 34,880
- Points
- 113
- Thread Author
- #1
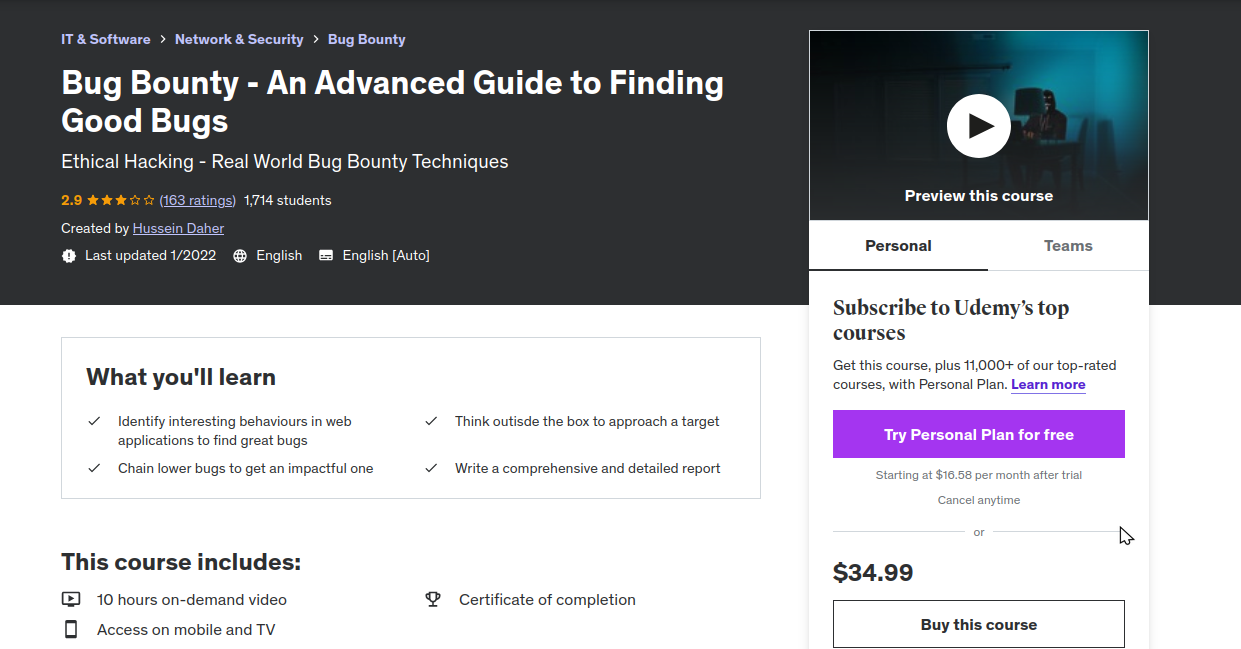
Bug bounties are evolving year after year and thousands of infosec enthuasiasts are looking to join the boat. Having a great place on that boat requires dedication and investing a great amount of time of work. In fact, there are multiple types of vulnerabilities and mastering the most important of these can be a game changer. In this class, attendees will learn the "how" and "why" of vulnerabilities they are already aware of instead of sticking to what the vulnerability is in general. This class will be based on real-life scenarios to show how to think out of the box in different scenarios to bring in the maximum impact.
During the session, students will have hands on excercises with:
During the session, students will have hands on excercises with:
- SQL Injection
- XXE
- SSRF
- RECON out of the box
- RCE
- SSTI
- Directory Traversal
- Access Control Vulns
- Authentication Issues
- Cache Poisoning
- Info Disclosure
- More subjects to be treated
Who Should Attend This Course
This course is intended for students with an interest in bug bounties, web vulnerability discovering and exploitation, or general infosec enthusiast who whish to know more about the side of bug bounties. Students should be comfortable with the type of vulnerabilities mentionned because we are not going to cover from a totaly beginner's side.
Key Takeaways
This course is intended for students with an interest in bug bounties, web vulnerability discovering and exploitation, or general infosec enthusiast who whish to know more about the side of bug bounties. Students should be comfortable with the type of vulnerabilities mentionned because we are not going to cover from a totaly beginner's side.
Key Takeaways
- Students will learn in-depth about a vulnerability exploitation
- Students will be able to approach a target effectively
- Students will learn thinking out of the box in different scenarios
Who this course is for:
- Bug bounty hunters and anyone interested into web application security
- Pentesters
- Hackers
To see this hidden content, you must reply and react with one of the following reactions :Like